Risk-Adaptive Onboarding & Verification Experience
Designing a compliance-grade decision platform that balances growth, trust, and risk
Summary
At scale, compliance systems often optimize for risk elimination instead of legitimate user enablement. Our onboarding pipeline routed all users, regardless of risk through heavy verification, ambiguous suitability questions, and email-based status updates. This created false rejections, operational overload, and delayed funding.
I led the redesign of a risk-adaptive, state-driven onboarding system that preserved full regulatory integrity while dynamically adjusting friction based on user risk.
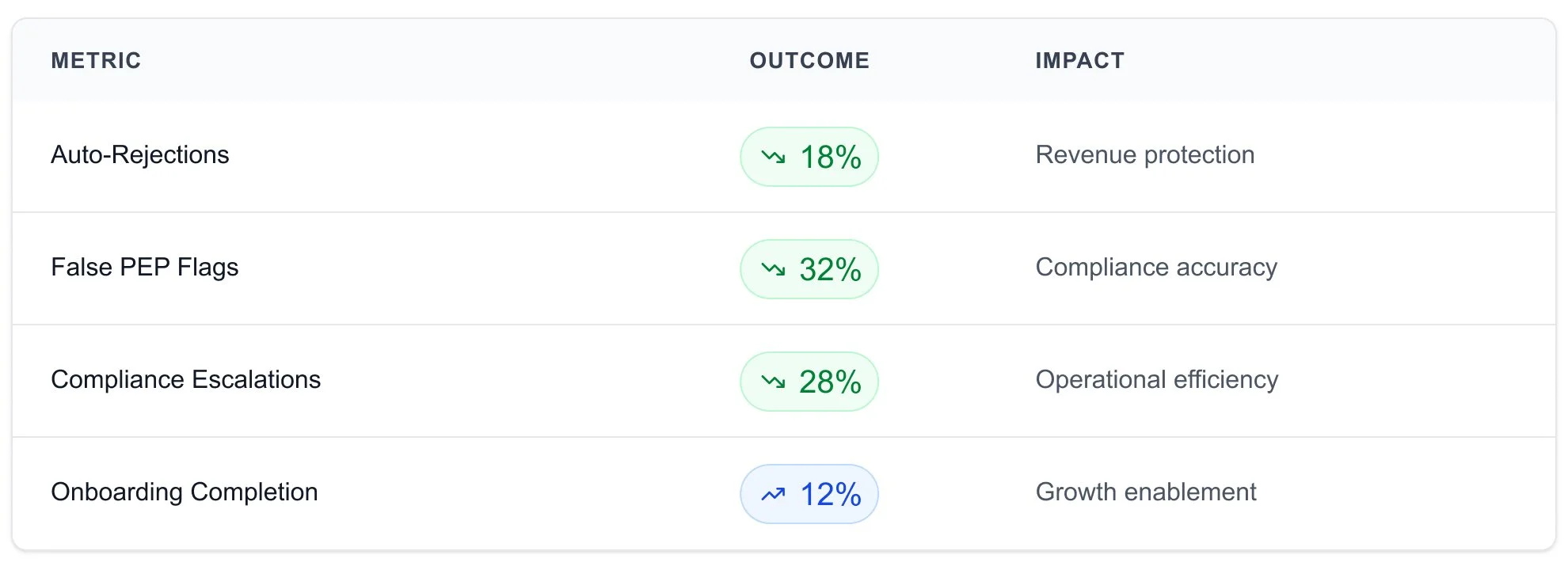
Business Impact
18%
Reduced unnecessary auto-rejections
32%
reduction in false PEP declarations
28%
reduction in compliance escalations
12%
increase in onboarding completion and funding progression
-
My Role
Lead UX Designer
-
Duration
3 Months
-
Markets
Australia & SVG
-
Team
Product Owners, Compliance, Risk, Engineering, Payments, and Operations teams.
The Business Tension
Growth needed faster funding. Compliance needed stricter controls. The UX system forced both to lose.
Structural Problems
One-size-fits-all verification
All users routed through heavy verification regardless of risk profile
Backend states hidden in email
Status updates not visible in-product, creating confusion
Compliance Noise
True high-risk cases masked by false positives
Suitability Assessment System
Financial knowledge & risk tolerance evaluation
Ambiguous financial and PEP questions
Leading to self-disqualification by legitimate users
Manual reviews scaling faster than onboarding
Operations team overwhelmed with low-risk escalations
What Was at Risk
Lost Revenue
Delayed funding preventing users from trading
Rising Operational Cost
Cost per user increasing with manual reviews
User Trust Erosion
Legitimate users feeling blocked without clear reason
My Scope
I owned the end-to-end experience architecture across multiple backend systems
Financial Knowledge (PKA) Logic
Product knowledge assessment & retry flows
PEP Declaration Framework
Politically exposed person screening & validation
Post-Signup Verification Routing
Risk-based identity verification pathways
Regulatory Intent Map
I created this to resolve inconsistent interpretations of compliance requirements across Product, Risk, and Engineering, which were slowing decisions and producing fragmented UX. The map translates regulatory language into a shared set of design principles, system states, and validation rules, giving teams a single source of truth that reduces stakeholder conflict, accelerates reviews, and ensures every UX decision remains auditable, scalable, and regulation-safe across entities.
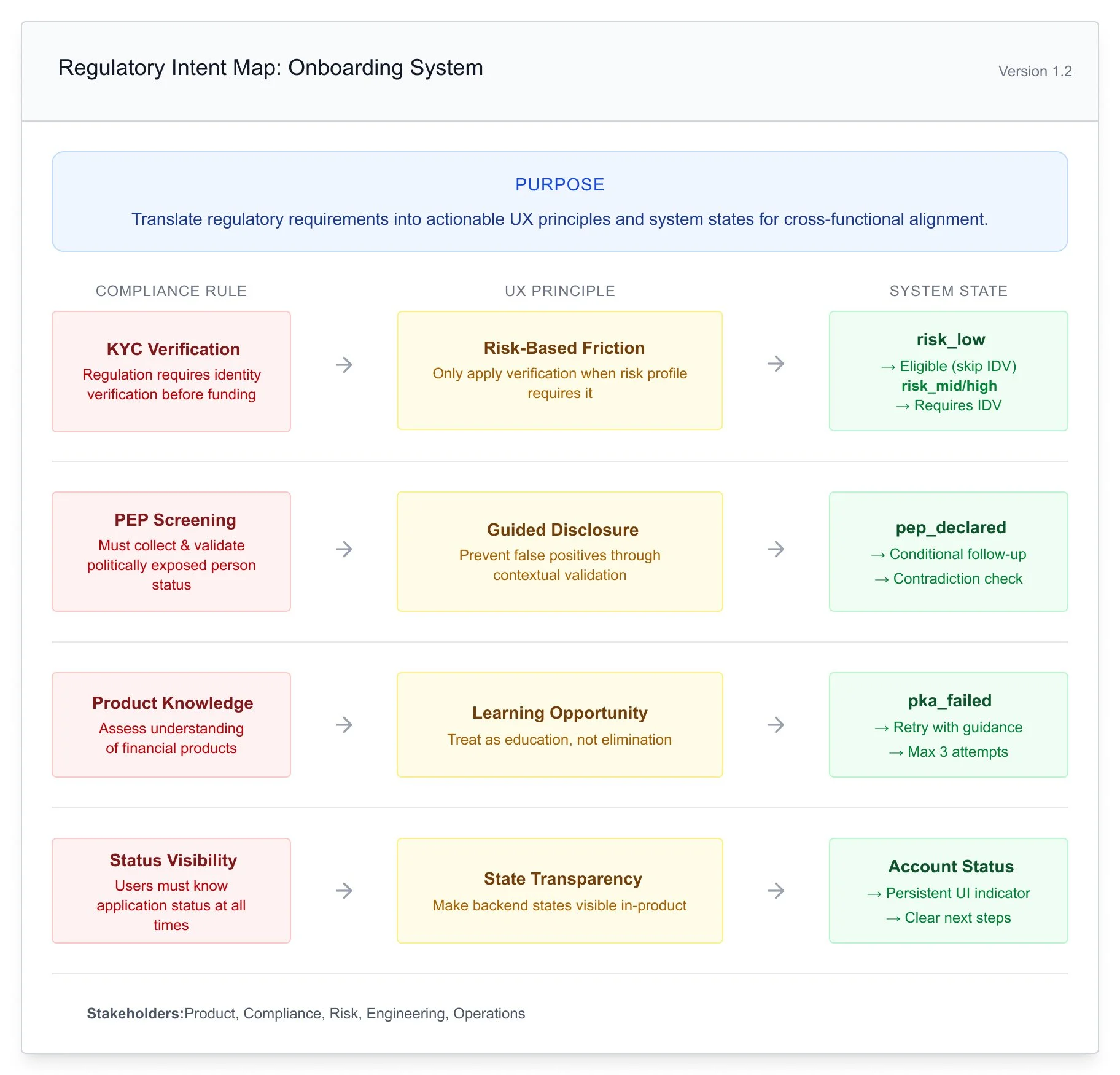
Strategic Design Principles
Design onboarding as a decision platform, not a form flow.
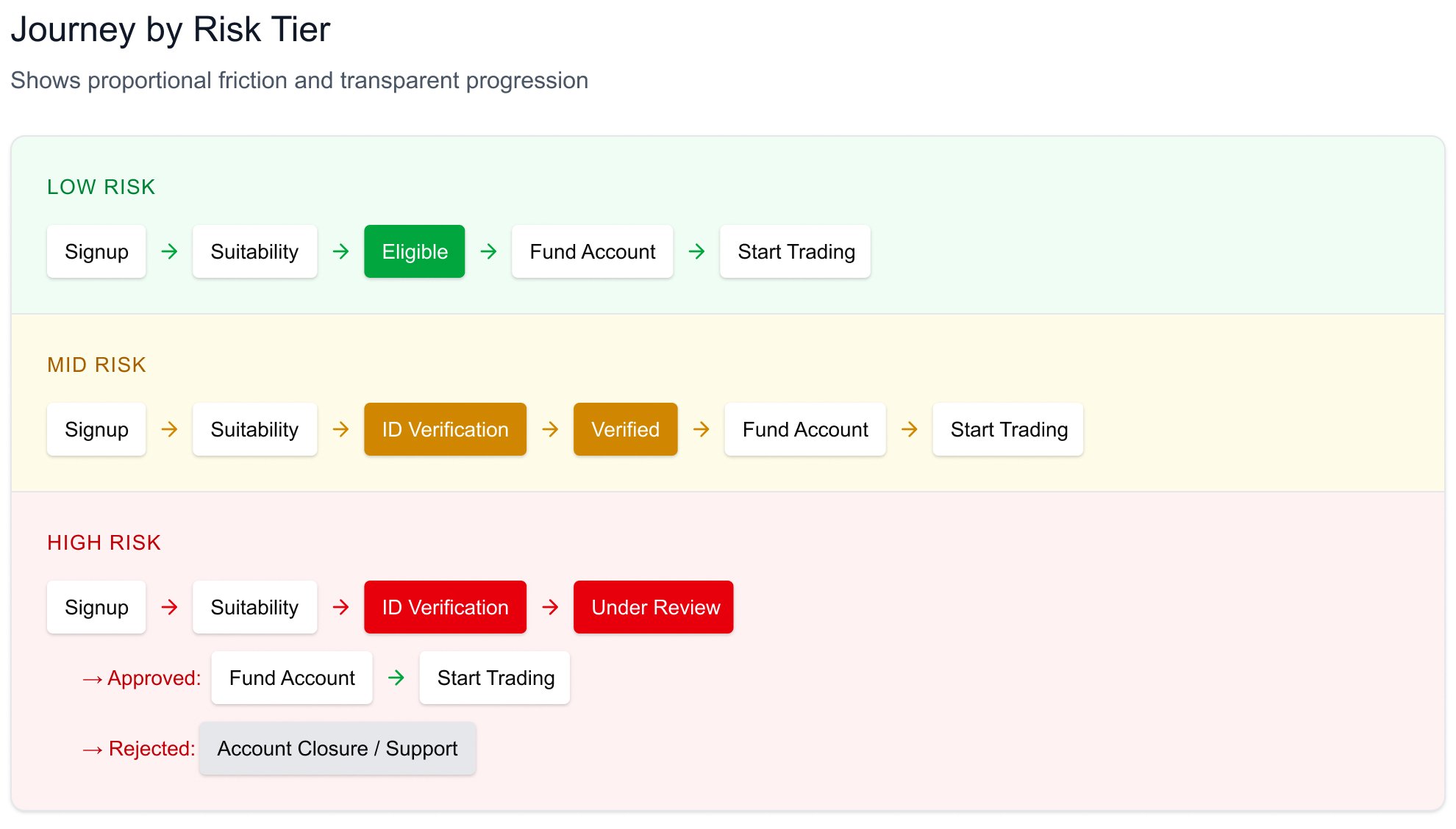
Risk-Based Progression - Friction should scale with user risk, not default severity.
I used backend risk classification as a routing signal at the decision layer, applying verification only when thresholds were met instead of defaulting all users into the same flow. This reduced unnecessary friction, lowered compliance workload, and improved legitimate user conversion.
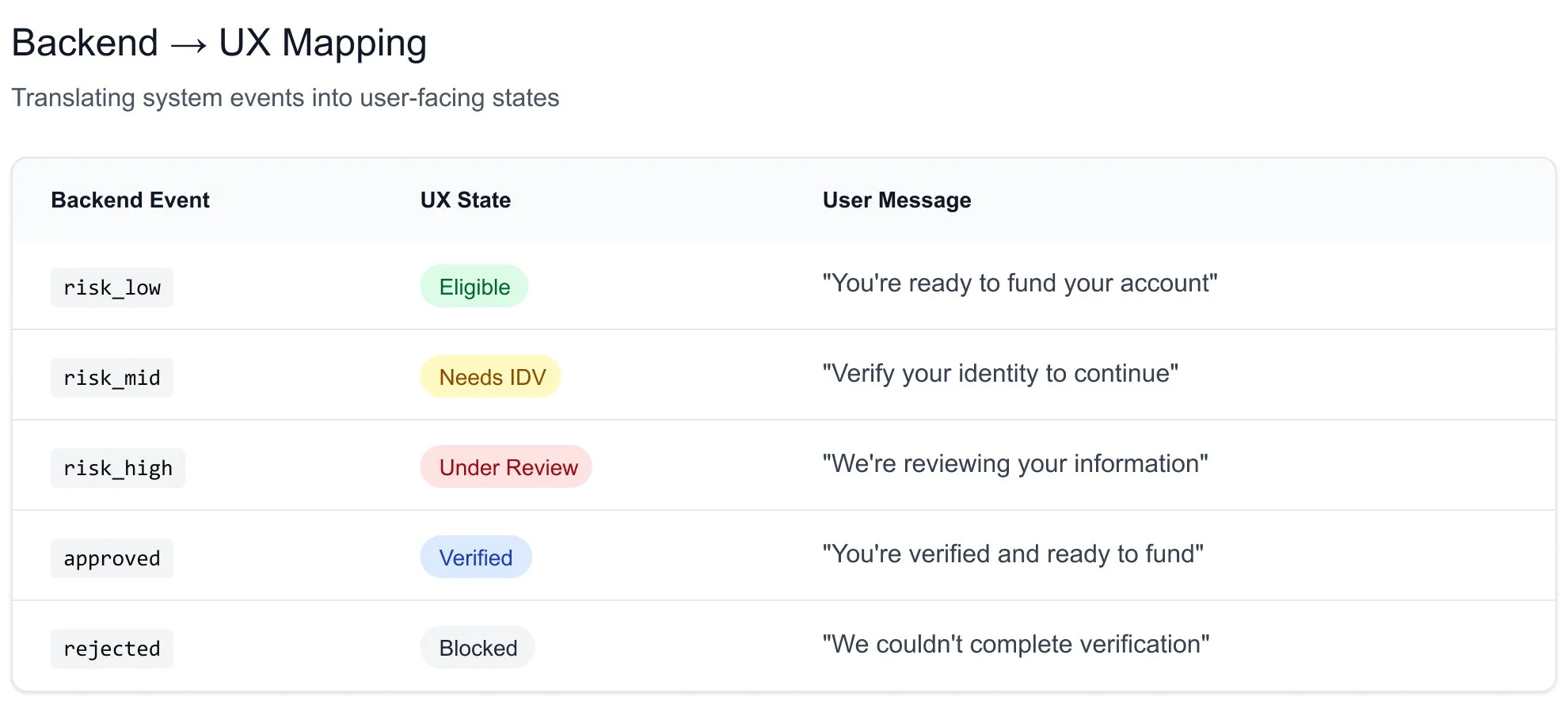
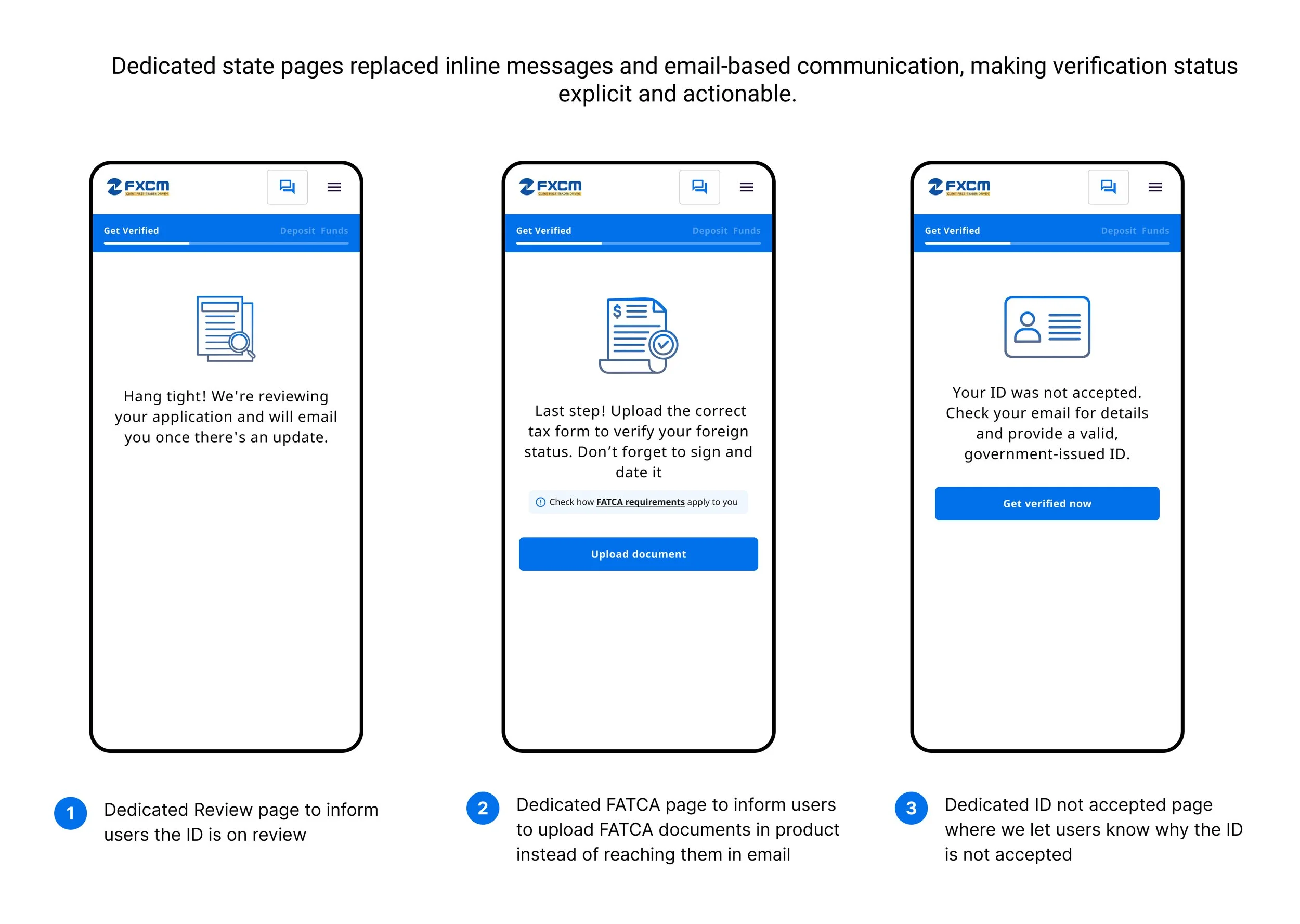
State-Driven UX - Every backend outcome must be visible in-product.
I mapped every backend outcome to a persistent, in-product status instead of email updates, making system decisions visible and predictable. This reduced user anxiety, cut support tickets, and aligned users, support, and compliance around a single source of truth.
Momentum Preservation - Eligible users should move toward funding without artificial friction.
I routed low-risk users directly to funding and guided higher-risk users through structured verification paths rather than hard stops. This maintained forward progress, minimized abandonment, and improved trust and completion rates. We routed low-risk users directly to funding and next actions, while guiding higher-risk users through structured, transparent verification paths instead of hard stops. This maintains forward progress for legitimate users, minimizes abandonment at critical moments, and ensures compliance checks feel like guided steps rather than blockers, improving both trust and completion rates.
Solution Architecture
I redesigned the onboarding system as a risk-adaptive, state-driven flow architecture where backend risk signals and compliance logic dynamically shape user progression instead of forcing everyone through a single linear path. By restructuring key flows routing, suitability, and PEP validation into modular, branch-based systems, I simplified handoffs between services, improved data quality for downstream risk engines, and created a scalable foundation that supports multiple risk tiers and regulated entities without requiring backend re-architecture.
1. Risk-Based State Model
PROBLEM
For SVG clients, the system required ID and address verification for all users regardless of risk level, which created unnecessary friction for low-risk users and significantly delayed time-to-funding.
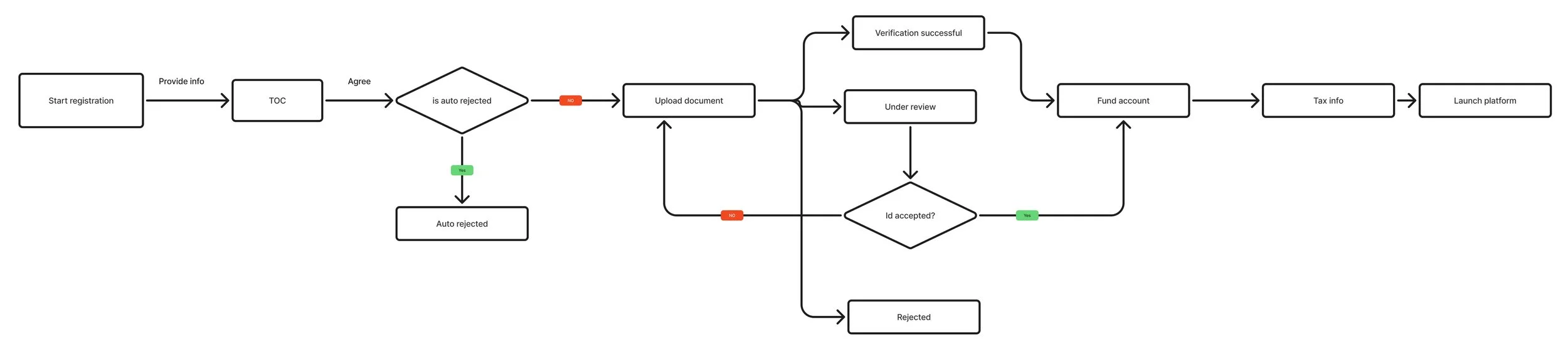
SOLUTION
I introduced a risk-adaptive state model that visualizes how backend risk signals drive user progression, clearly separating low-, mid-, and high-risk paths so the system’s decision logic becomes transparent, auditable, and easier to optimize.
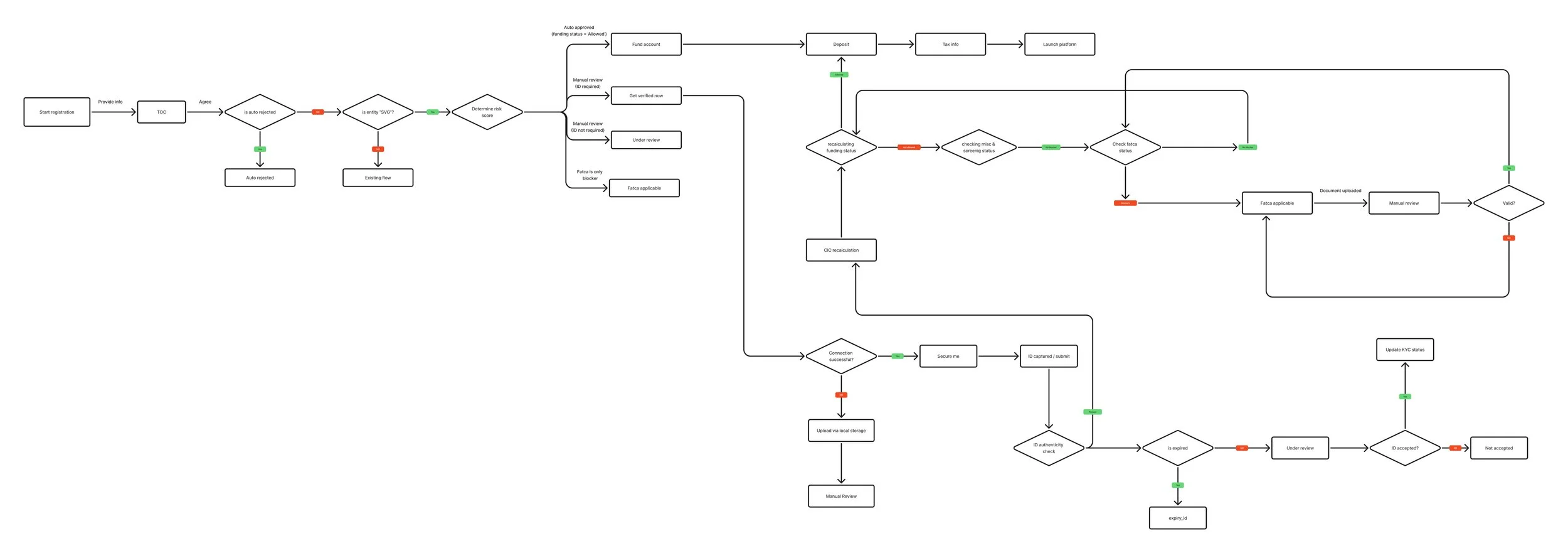
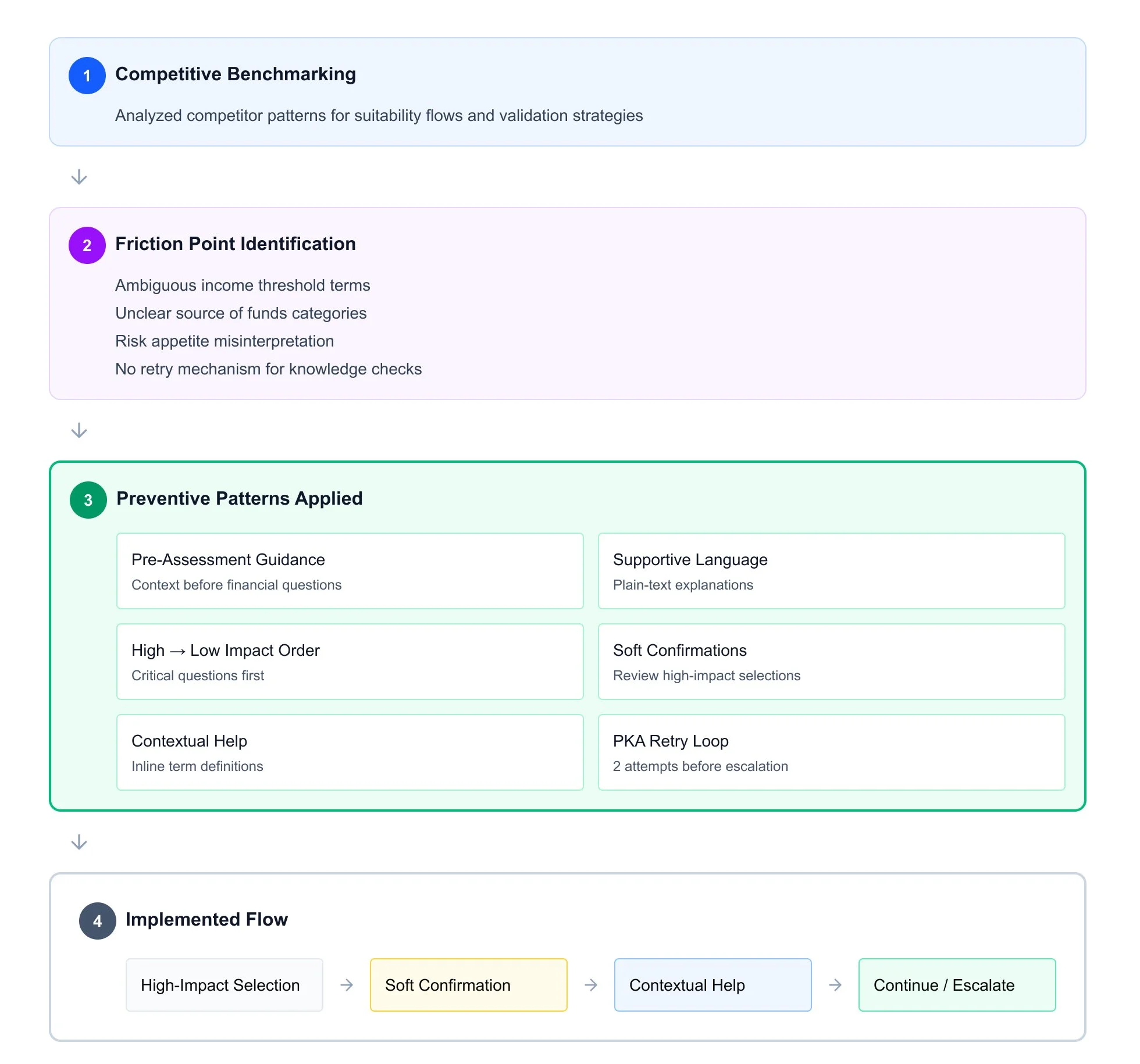
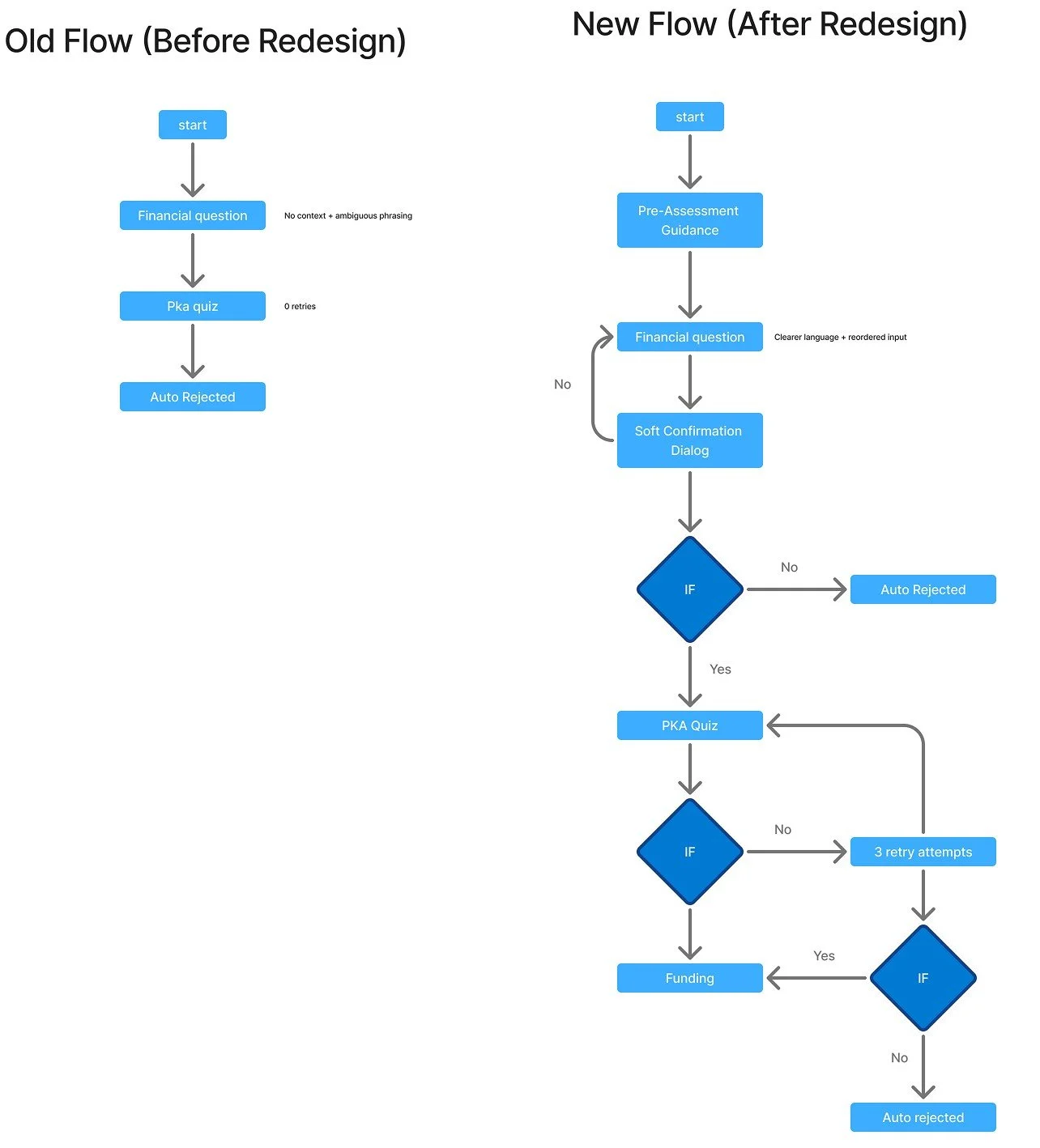
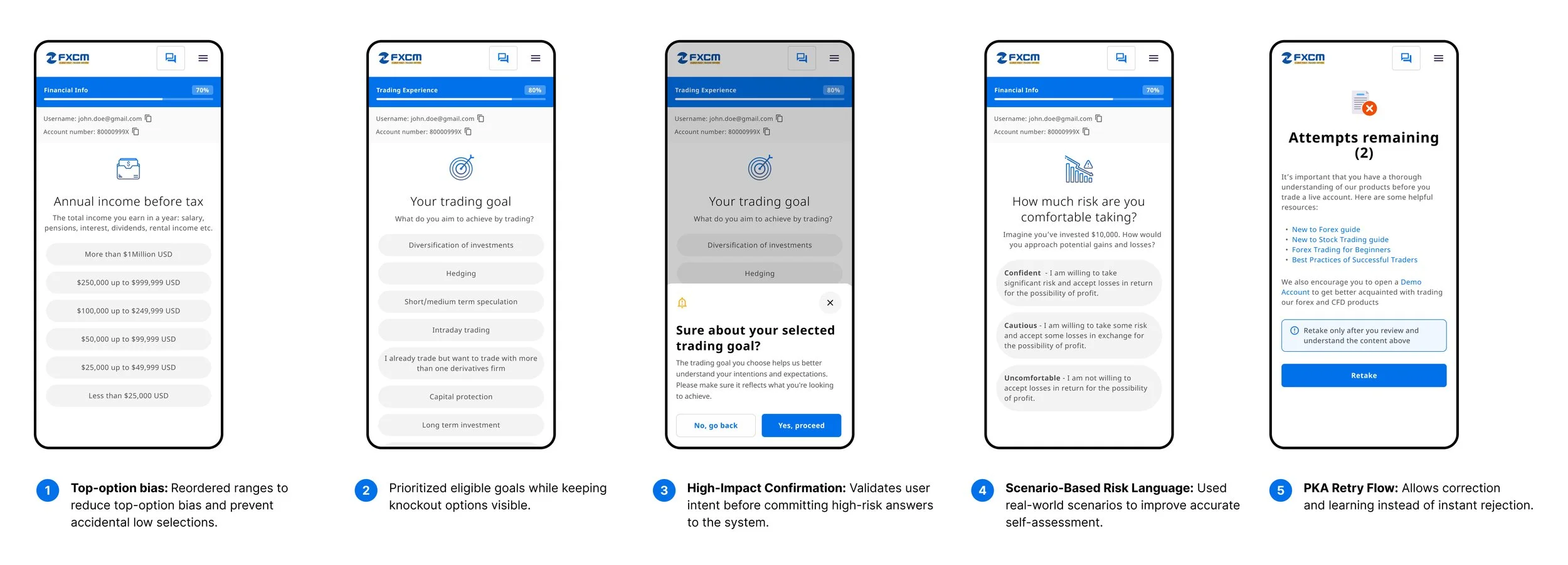
2. Minimizing AU Auto-Rejections
PROBLEM
In the AU entity, users were being auto-rejected due to misunderstood high-impact financial selections (e.g., income thresholds, source of funds, risk appetite), even when they were otherwise legitimate. This created conversion loss, increased manual compliance reviews, and added high cognitive pressure in a compliance-heavy flow.
SOLUTION
I designed a preventive suitability architecture informed by competitor benchmarking and internal friction analysis. Using patterns like pre-assessment guidance, supportive financial language, high → low impact ordering, and retry loops instead of hard failures, I rebuilt the flow to introduce soft confirmations for high-impact inputs, contextual help for ambiguous terms, and a structured PKA retry mechanism. This shifted the system from instant rejection to progressive validation, allowing users to correct misunderstandings before triggering irreversible compliance actions and improving funding completion and funding rate without weakening regulatory controls.
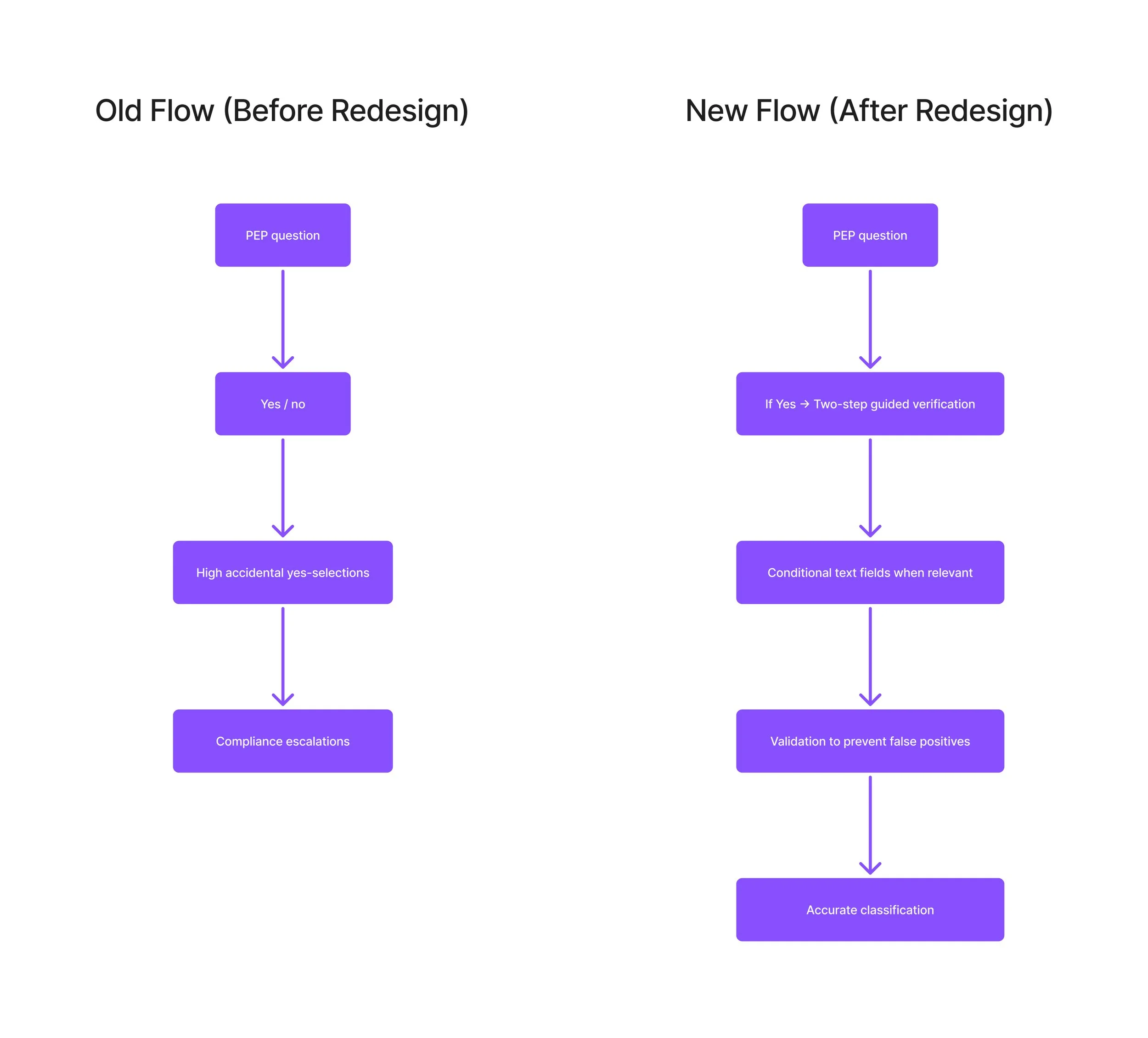
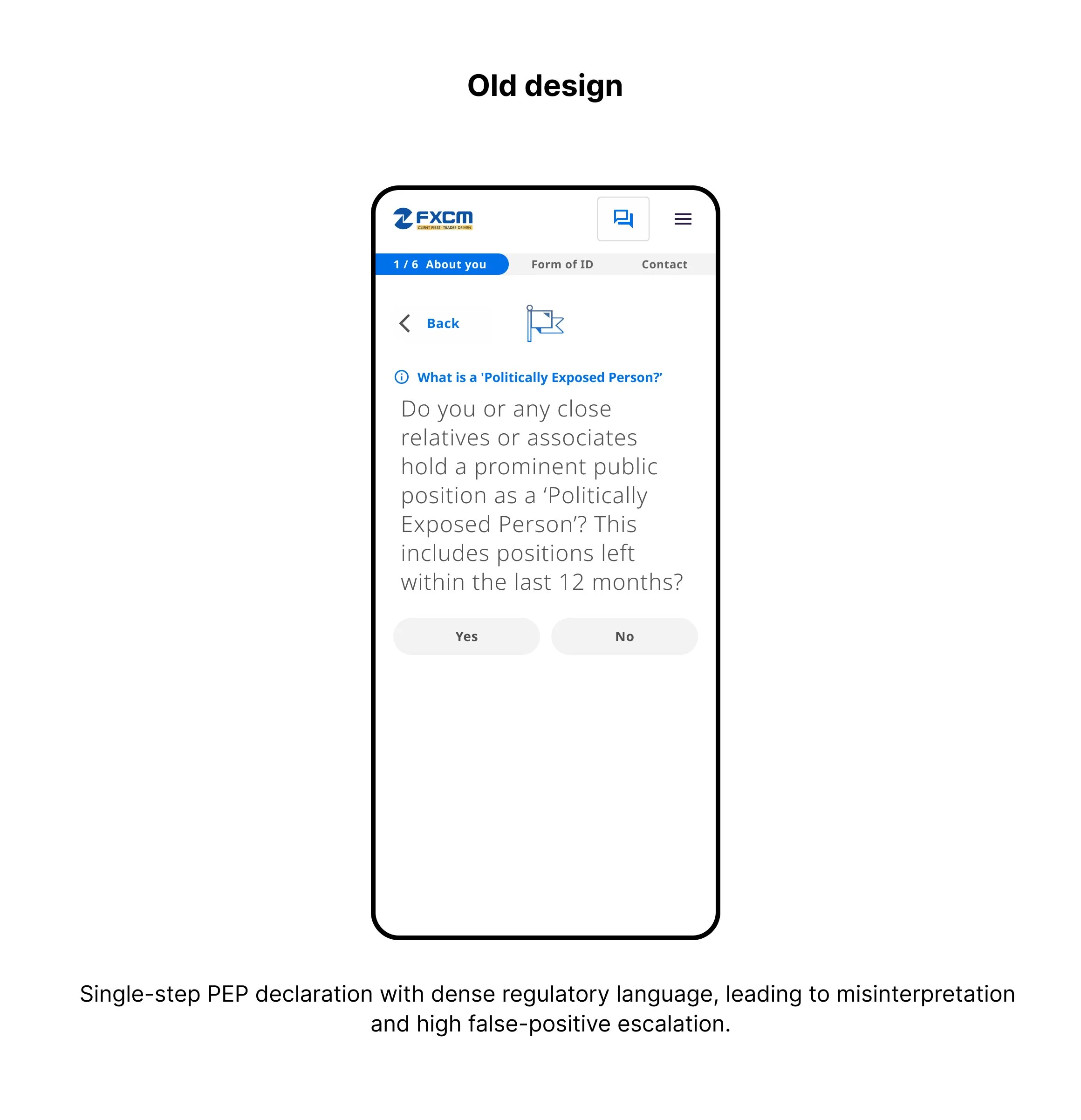
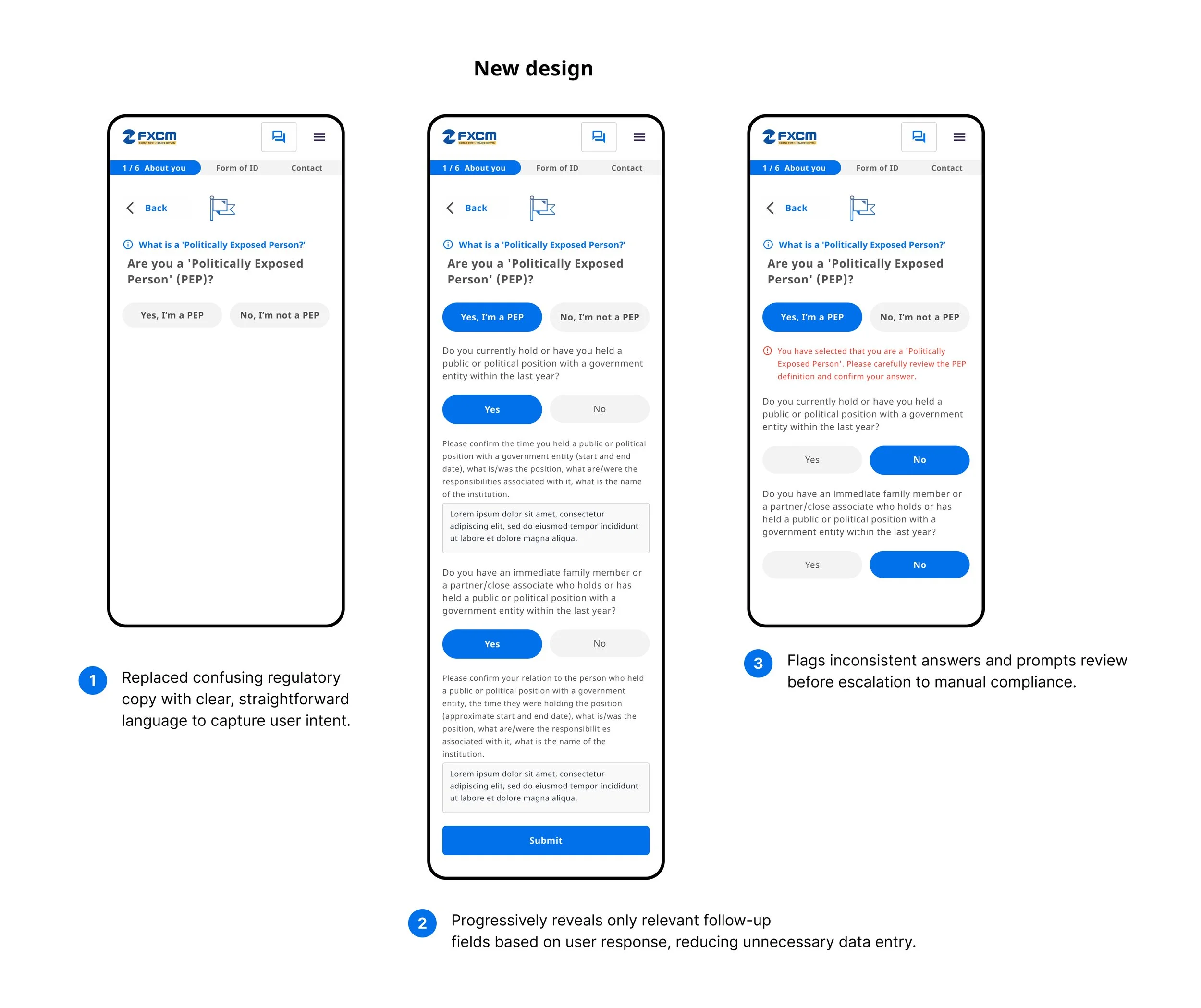
3. Compliance Decision Tree (PEP)
PROBLEM
The original PEP flow relied on a single Yes/No declaration that escalated many legitimate users into manual compliance review due to misunderstanding of the Politically Exposed Person definition. This created false positives, increased operational workload, and delayed onboarding for low-risk users.
SOLUTION
I redesigned the flow into a conditional, branch-based decision tree that introduces targeted follow-up questions and contradiction validation before escalation. This ensures only genuinely high-risk cases are routed to manual review while preserving a clear, auditable trail for compliance.
Design Decisions
Three core interventions targeting the highest-impact friction points, designed for measurable outcomes within a single release cycle.
Decision 1 - Risk-Adaptive Routing Layer
The "Congratulations" screen became a routing engine, not a confirmation page
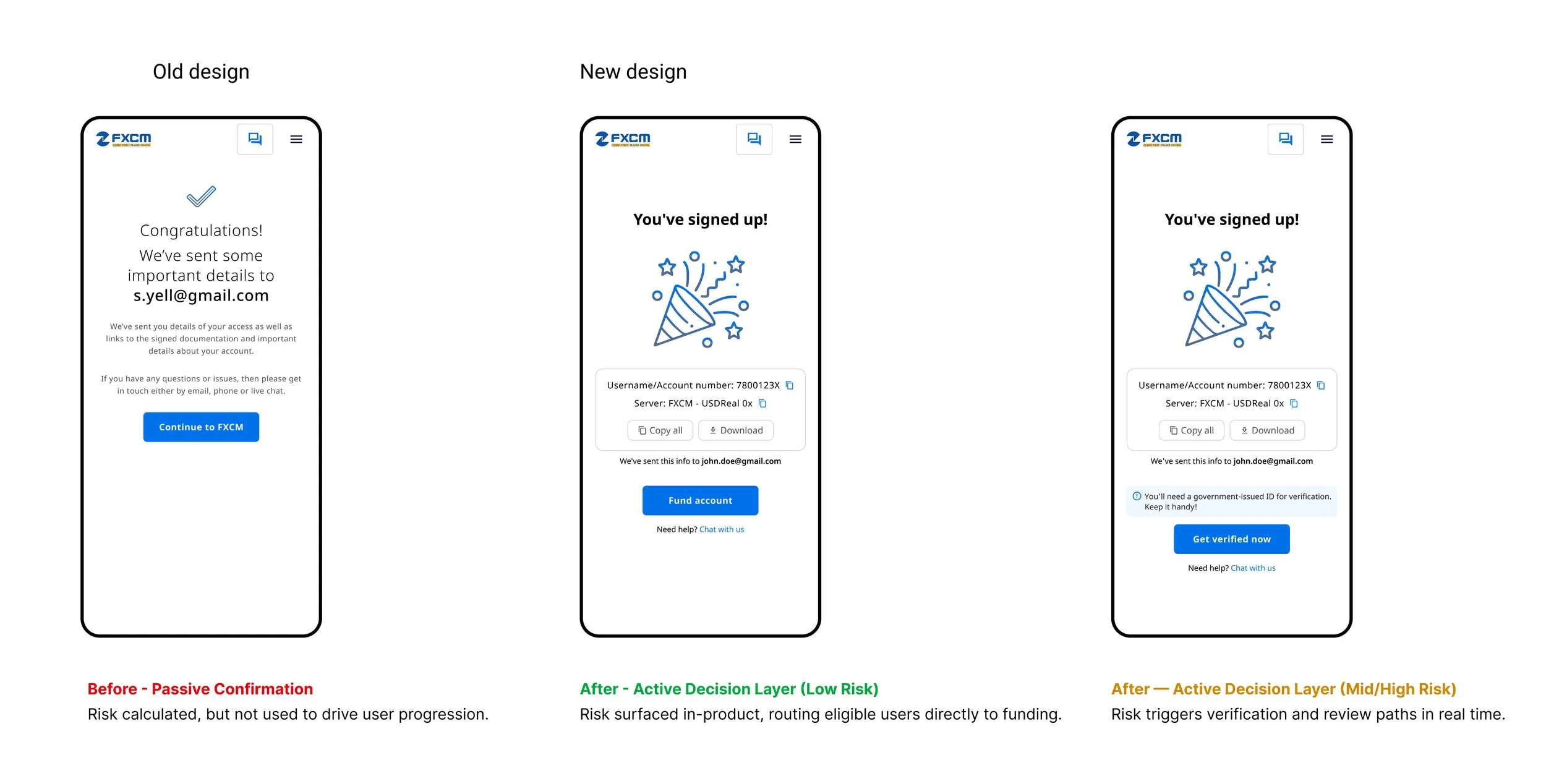
Why It Matters
Reduced unnecessary verification
Made system decisions transparent
Preserved backend risk logic
Decision 2 - Suitability as Guided Disclosure
PROBLEM
High-impact suitability questions were presented without context or confirmation, leading users to make irreversible selections that triggered false rejections and unnecessary compliance escalation.
SOLUTION
I introduced guided disclosure at the point of decision adding pre-assessment framing, soft confirmations for high-impact answers, and structured retries—so users could validate intent before the system committed their input to a compliance outcome.
Decision 3 - Conditional PEP Validation
PROBLEM
PEP was captured as a single Yes/No choice, causing users to misinterpret the definition and unintentionally trigger high-risk escalation and manual compliance review.
SOLUTION
I introduced conditional disclosure at the point of decision adding targeted follow-up questions and contradiction validation so user intent is clarified before the system commits the case to escalation. This ensures only genuinely high-risk profiles are routed to Compliance while keeping the flow transparent and auditable..
Technical Constraints & Trade-Offs
Technical Constraint
Suitability and PKA systems could not be merged at the backend due to regulatory audit requirements and separate compliance ownership.
Design Decision
Unified mental model for users
Independent audit trails per system
Full compliance traceability
Trade-Off
Slight UX complexity vs full system re-architecture risk.
Results & Business Impact
Across AU and UK onboarding journeys, the redesign delivered measurable improvements in conversion, data quality, and operational efficiency.
Reduction in Auto-Rejections
18%
Fewer users incorrectly rejected from onboarding
Reduction in False PEP Flags
32%
Decrease in accidental compliance declarations
Increase in Onboarding Completion
12%
Users completing verification and funding

Reflection
"This project reinforced that in regulated onboarding, clarity at the decision layer matters more than adding safeguards downstream.”
By making risk states and next steps visible in-product, I reduced confusion, prevented false escalations, and improved funding progression without changing backend risk logic.
Key Takeaway
Designing UX as a risk and compliance interface not a form flow drives both conversion and operational efficiency.
What Failed
Our first rollout surfaced too many system states and edge-case messages at once, which increased cognitive load and slowed user progression especially for low-risk users who only needed a clear path to funding. Funnel analysis showed confusion around status transitions, so I consolidated the experience into three primary states (Eligible, Needs Verification, Under Review) and deferred secondary compliance details behind progressive disclosure. This improved clarity without weakening regulatory traceability.
Partnering early with Compliance and Risk to translate regulatory intent into clear UX rules and system states
Using risk-tier routing to apply verification only where it added real compliance value
Adding preventive validation (soft confirmations, retries) to reduce false rejections
Instrumenting drop-off and escalation by risk tier to guide iteration
What Worked
What I Learned
Surfacing system state builds trust faster than adding more automation
Small decision-level changes (copy, ordering, confirmation) can materially impact funding and escalation rates
Metrics framed by risk tier accelerate alignment with Legal and Compliance more than aggregate conversion data
Scalable compliance UX depends on shared mental models, not just shared components